Many of us have families to look after. We save money not only for our own future but also – perhaps even more so – for our kids and grandkids. We want to secure a good education, help them buy a home or simply set aside something for when they need it.
So did Tony. He’d saved a substantial amount for his sons' future, more than $4 million in bitcoin. And with just one click, he lost it all to vishing, a type of scam that uses phone calls to trick people into giving up sensitive information.
Scammers posed as Google Support agents and, after an elaborate scheme, first caught his attention, then gained his trust and ultimately left him with nothing.
"Please, man. Is there anything you can do to give me something back?" was Tony’s final, desperate plea to the scammers, hoping to appeal to their humanity.

A man typing on his computer keyboard (Kurt "CyberGuy" Knutsson)
What is vishing?
Vishing, short for "voice phishing," is a type of cybercrime that uses phone calls to deceive individuals into revealing personal or financial information. Unlike traditional phishing, which relies on emails or text messages, vishing leverages the power of human voice and social engineering to manipulate victims. Scammers often impersonate legitimate organizations, such as banks, tech companies, or government agencies, to gain trust and create a sense of urgency. They may ask for passwords, credit card numbers, or other sensitive details, which they then use for fraudulent purposes.
Because vishing relies heavily on social engineering tactics, it can be difficult to detect, making it a particularly dangerous form of cybercrime.
Illustration of a hacker at work (Kurt "CyberGuy" Knutsson)
BEST ANTIVIRUS FOR MAC, PC, IPHONES AND ANDROIDS - CYBERGUY PICKS
The scam is a well-orchestrated play
Let's break down these vishing schemes to understand why they are so effective. Once you see them as a staged play consisting of different acts, it becomes easier to recognize the individual tactics.
Act 1: The setup and targeting
Scammers start by identifying potential victims through social media, public transaction records, leaked databases, and more. Once they select a target, they gather personal details (email, phone number, financial holdings) to build credibility. And you could easily be a target. That’s because data brokers – companies that buy and sell your personal information – are goldmines for scammers. Your entire profile is likely out there, containing everything they need to run a successful scam: your name, address, contact details, family members, owned properties and more.
How to protect yourself at this stage:
- Limit what you share online, especially financial details
- Sign up for data removal services that erase your personal information from company databases
Act 2: The first contact
Scammers always initiate contact first. Let’s walk through a vishing scam using a Google account as an example.
- Triggering a real security alert: Scammers may attempt to recover your Google Account to prompt real security alerts, like verification codes sent to your phone. Their goal isn’t to reset your password but to make you believe there’s a real security issue.
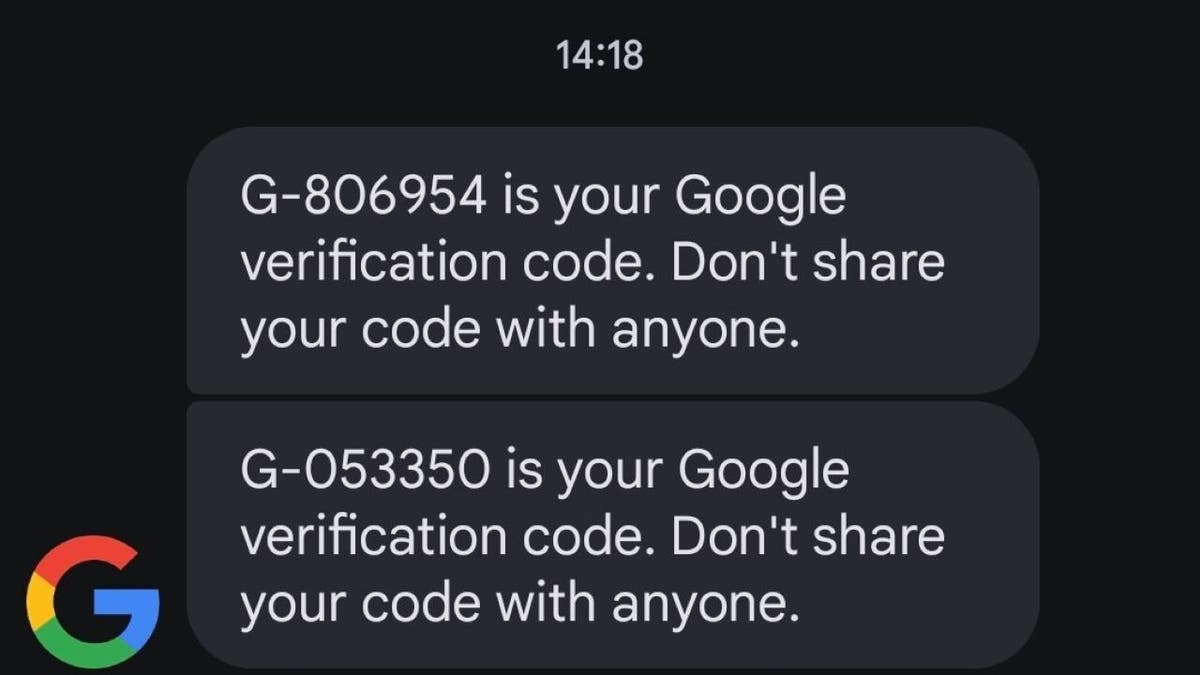
Google verification code text (Kurt "CyberGuy" Knutsson)
- Sending a fake security message: They create a fake Google Form using your email address, designed to mimic an official security alert. The message often claims there’s been a security breach and that a named support agent will contact you soon.
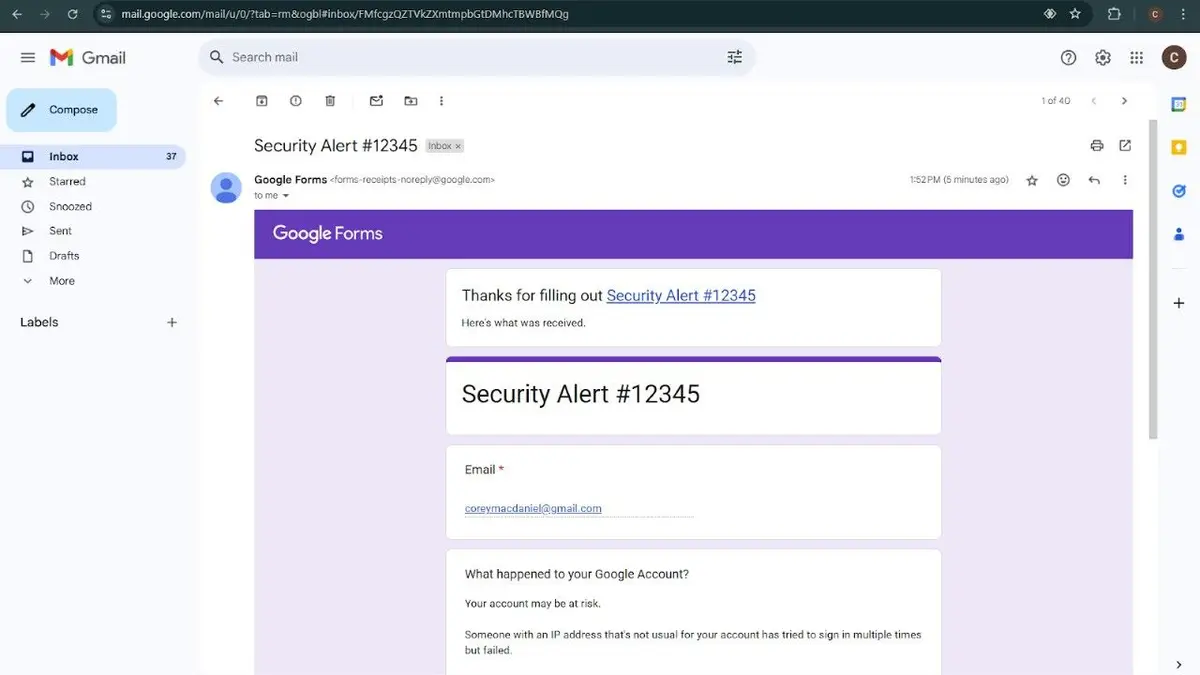
Fake Google form (Kurt "CyberGuy" Knutsson)
- Placing a call: Shortly after you receive the email, scammers call using a spoofed Google number, guiding you through fake security steps.
How to protect yourself at this stage:
- Pause and verify – Real companies don’t call or email you for sensitive security actions
- Contact the company directly – Use official contact details (don’t trust the caller’s number or email)
- Be skeptical of urgent security warnings – Scammers create fake emergencies to make you act without thinking
HOW TO REMOVE YOUR PRIVATE DATA FROM THE INTERNET
Act 3: Building trust
Scammers no longer ask for passwords outright. That trick doesn’t work anymore. Here's what they do instead.
- Introducing themselves as support agents: They remain calm and friendly, claiming they’re here to help investigate the issue. They reference details from the fake Google Form to seem legitimate.
- Walking through a real password recovery process: While on the phone, scammers instruct you to change your password as a security measure. They don’t send any suspicious links but instead guide you through the real recovery process. At this point, they still don’t have access to your account. But that’s about to change.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?

Illustration of username and password credential page (Kurt "CyberGuy" Knutsson)
Act 4: The scam
After you successfully reset your password, scammers ask for one final step: log in. This is where the real scam happens.
- Sending a phishing link: Now that you trust them, they send a message using a spoofed Google number with a link to log in. However, the link leads to a phishing site designed to look like Google’s login page.
- Logging into the real site: As soon as you enter your credentials into the fake page, scammers input them into the real Google site. Seconds later, you receive a genuine Google security prompt asking, "Is this you?"
- Clicking "Yes, it’s me" completes the scam: While you were on their fake platform, they were simultaneously logging into your real account using your credentials. The Google security prompt? It wasn’t for your device. It was for theirs. As a result, you've just given scammers access to your account.
How to protect yourself at this stage:
- Never log in to your accounts using links that were sent to you
- Always check the URL before entering credentials and look for "https://" and correct spellings
- Use a password manager that autofills only on legitimate sites. A high-quality password manager ensures security with zero-knowledge encryption, military-grade protection and support for multiple platforms, including Windows, macOS, Linux, Android, iOS and major browsers. Look for features like unlimited password storage, secure sharing, password health reports, data breach monitoring, autofill and emergency access. Check out my expert-reviewed best password managers of 2025 here
THE HIDDEN COSTS OF FREE APPS: YOUR PERSONAL INFORMATION
Act 5: The heist
At this stage, the scammers end the call, leaving you feeling at ease. You won’t realize what happened until it’s too late. And it’s not just Google accounts at risk. The same method can be used to access Apple accounts, banking services and cryptocurrency wallets. For some, losing access to Google alone is devastating; after all, Google Drive, Google Photos and other cloud services store vast amounts of personal and financial data. But by the time you realize what’s happened, it’s already too late.
How to protect yourself at this stage:
- Secure your accounts immediately – Reset your passwords, enable two-factor authentication with an authenticator app and log out of all active sessions to remove unauthorized access.
- Report and monitor for fraud – Alert your bank, credit card provider or crypto exchange to freeze transactions if needed. Report the scam to the FTC (reportfraud.ftc.gov), IC3 (ic3.gov) and the affected platform. Monitor your accounts for suspicious activity and consider a credit freeze to prevent identity theft.
While securing your accounts and reporting fraud are crucial after a scam has already occurred, the best defense is preventing these attacks in the first place. Taking these steps can help ensure you don’t fall victim to a vishing scam in the first place.
How to protect yourself from vishing scams
1. Invest in personal data removal services: These scams all have one thing in common: they need some of your personal info to work. Without your name, phone number or email, these scams can't happen. Scammers might even try to gain your trust by sharing more of your personal info, like your Social Security number, to seem more believable. I strongly suggest you remove your personal info from people search sites online. If you give someone your email or phone number, they might be able to find your home address through a reverse search. While no service promises to remove all your data from the internet, having a removal service is great if you want to constantly monitor and automate the process of removing your information from hundreds of sites continuously over a longer period of time. Check out my top picks for data removal services here.
2. Set up recovery contacts: Establish backup contacts for your accounts (Google, Apple and bank) to ensure you have a way to regain access if locked out.
3. Monitor financial accounts: Regularly check your financial accounts for any suspicious activity or unauthorized transactions.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
4. Enable two-factor authentication (2FA): Enable 2FA on all accounts, especially Google, Apple and financial services. This adds an extra layer of security, making it harder for scammers to access your accounts even if they obtain your login credentials.
5. Secure devices: Ensure your devices are secured with screen locks or biometric authentication and keep software up to date to prevent malware attacks.
6. Report scams promptly: If you've been scammed, report the fraud immediately to the FTC at reportfraud.ftc.gov and notify the affected platforms.
7. Use strong antivirus software: Install and regularly update strong antivirus software to protect your devices from malware, viruses and other cyber threats. Antivirus software provides real-time protection, scans for malicious files and helps prevent infections by blocking access to harmful websites and downloads. The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe. Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices.
Kurt's key takeaways
Tony's story is a chilling reminder that even the most diligent savers can fall victim to sophisticated scams. These vishing schemes, carefully orchestrated like a theatrical play, exploit our trust and leverage real security alerts to gain access to our accounts. Protecting ourselves requires constant awareness, skepticism towards unsolicited communications, and proactive measures to safeguard our personal information. While the tactics may evolve, the underlying principle remains the same: scammers rely on deception to exploit our vulnerabilities. By understanding their methods and taking preventative steps, we can make it harder for them to succeed.
CLICK HERE TO GET THE FOX NEWS APP
What more do you think companies and the government should do to combat this growing threat? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you'd like us to cover.
Follow Kurt on his social channels:
Answers to the most asked CyberGuy questions:
- What is the best way to protect your Mac, Windows, iPhone and Android devices from getting hacked?
- What is the best way to stay private, secure and anonymous while browsing the web?
- How can I get rid of robocalls with apps and data removal services?
- How do I remove my private data from the internet?
New from Kurt:
- Try CyberGuy's new games (crosswords, word searches, trivia and more!)
- CyberGuy's Exclusive Coupons and Deals
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt "CyberGuy" Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on "FOX & Friends." Got a tech question? Get Kurt’s free CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.
.png)
 12 hours ago
1
12 hours ago
1








 English (US) ·
English (US) ·